Articles, podcasts, webinars… and above all: practical advice! In short, a collection of resources to make your project a success.
Resources to get you started!


In the spotlight
News
18 March 2024
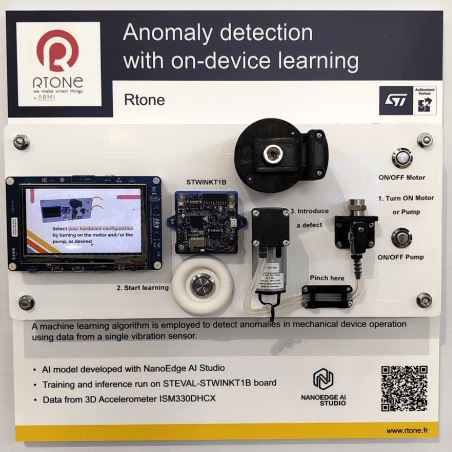
Embedded Machine Learning Demo
For the occasion of the Embedded World exhibition in Nuremberg, which takes place from April 9th to April 11th, 2024, we are offering a new demo resulting from our...
Our news

Product design
11 October 2023
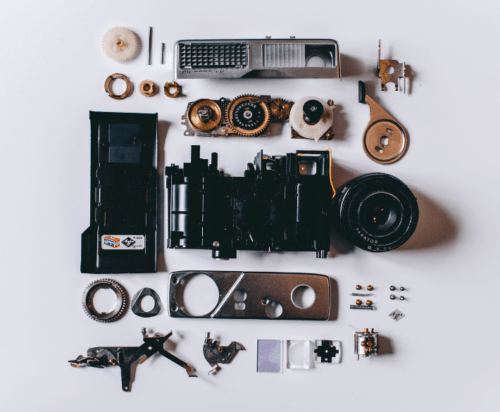
Make or Buy: how to design an innovative product?

IoT
20 February 2023
Geolocation: which technology to choose?
Sector
24 January 2023
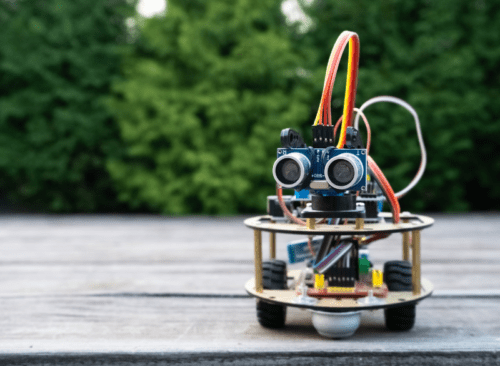
The essential skills for a robotics project

News
01 January 2023
Rtone joins forces with House of HR
News
13 September 2022
MicroEJ and Rtone join forces

IoT
08 August 2022
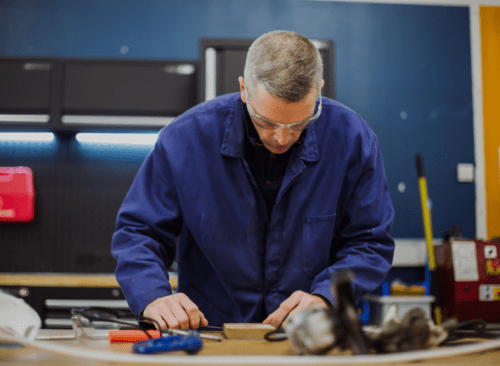
Embedded software, or how to build the heart of your product?
Industrialisation
21 June 2022
Industrialisation: product lifecycle management?

Product design
31 December 2021
EMC: how to survive its qualification tests?
Product design
30 September 2021
5 things to know when creating a prototype

News
09 September 2021
Rtone acquires industrialisation accelerator StartAndFab
Dive
the heart of projects
with our case studies
Discover the problems of your peers, the solutions provided by our teams and above all the results.